Shadow AI Security: What Australian Businesses Need to Know in 2026
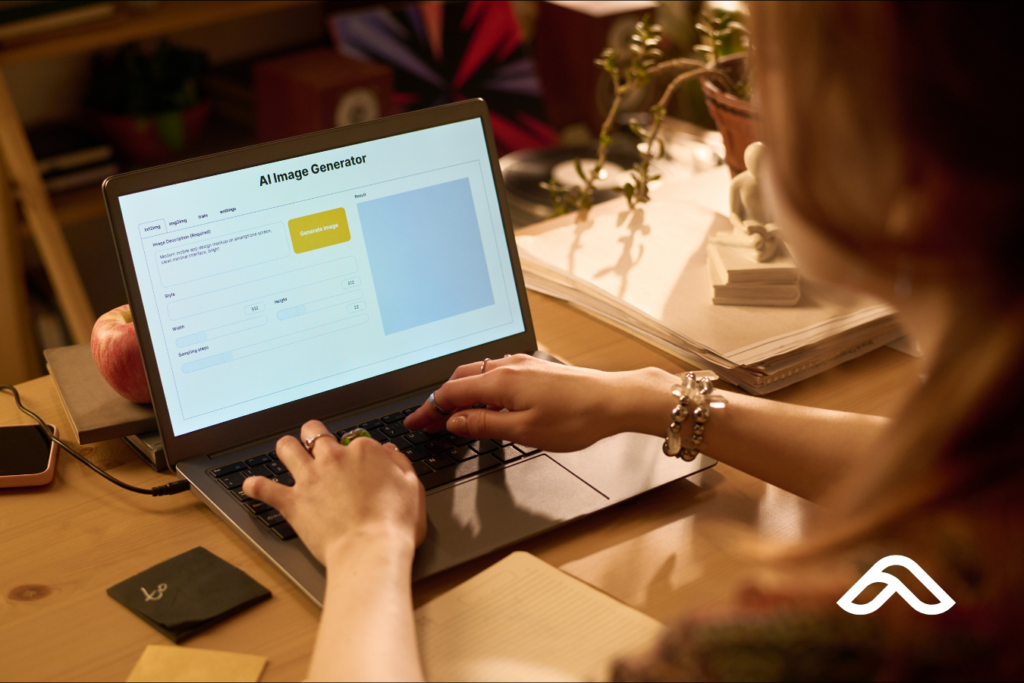
Shadow AI Security: What Australian Businesses Need to Know in 2026 Shadow AI security isn't a future problem. For most businesses, it's already happening — quietly, routinely, and…