
Security
Security


Safe and Secure File Storage and Transfer

Secure Data Backup: Best Practices to Protect Your Information
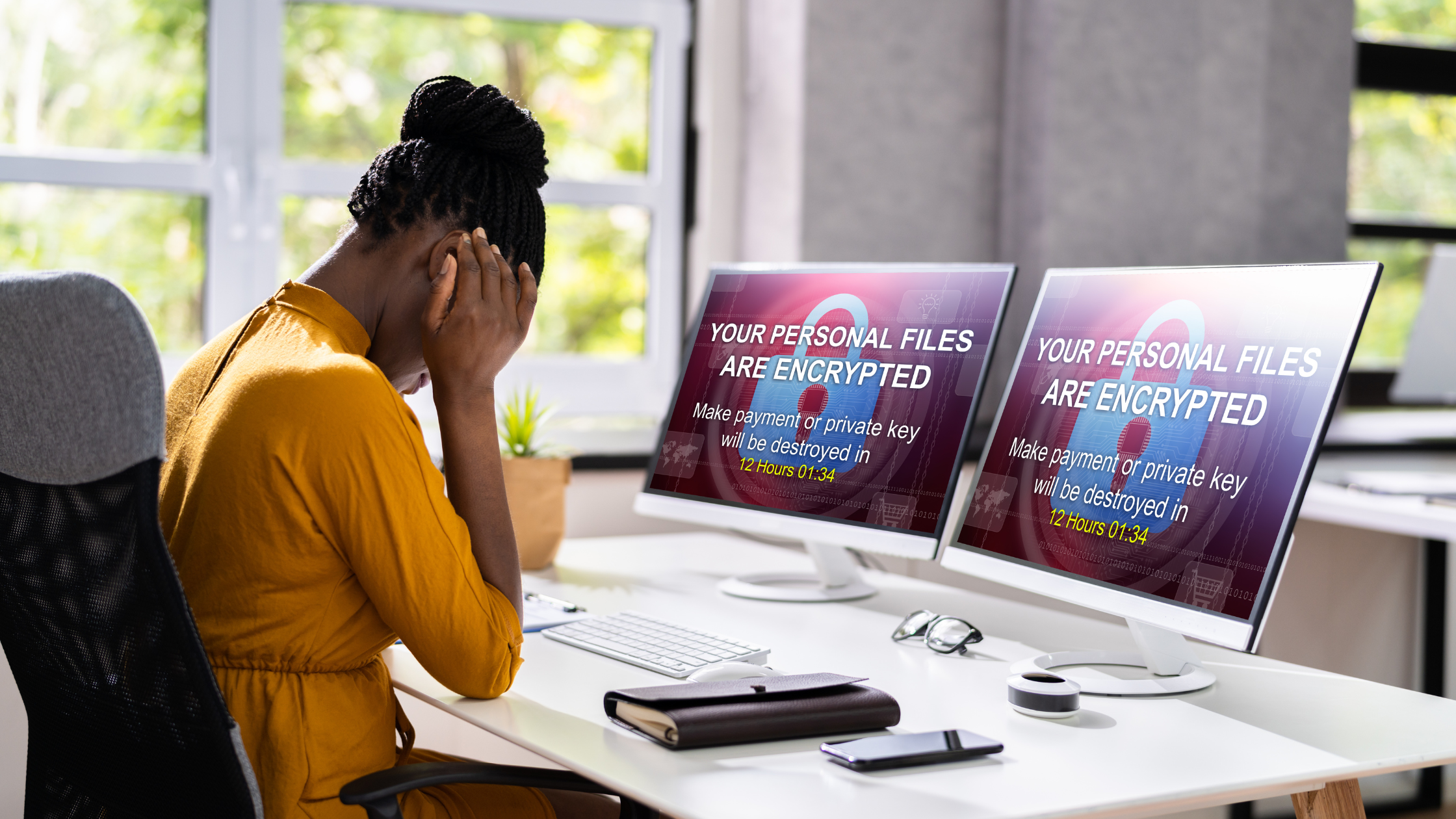
What to Do After a Personal Data Breach

IT Outsourcing Benefits: A Strategic Approach to Business Growth

Clearing Cookies: A Double-Edged Sword

Optimizing Your IT Infrastructure
Ransomware Attacks: Why Your Enterprise is a Target
Phishing 2.0: The AI-Powered Threat You Can’t Ignore

Signs That Your Smart Home Device Has Been Hacked

7 Common Pitfalls When Adopting Zero Trust Security: What to Avoid
